With the arrival of new legislation in the field of cybersecurity, the obligations of municipalities, cities, energy companies, and industrial enterprises have fundamentally changed. The NIS2 Directive and the subsequent Czech Cybersecurity Act impose on selected organizations not only the obligation to actively protect their systems but also to systematically record incidents and, in defined cases, report them to the National Cyber and Information Security Agency (NÚKIB).
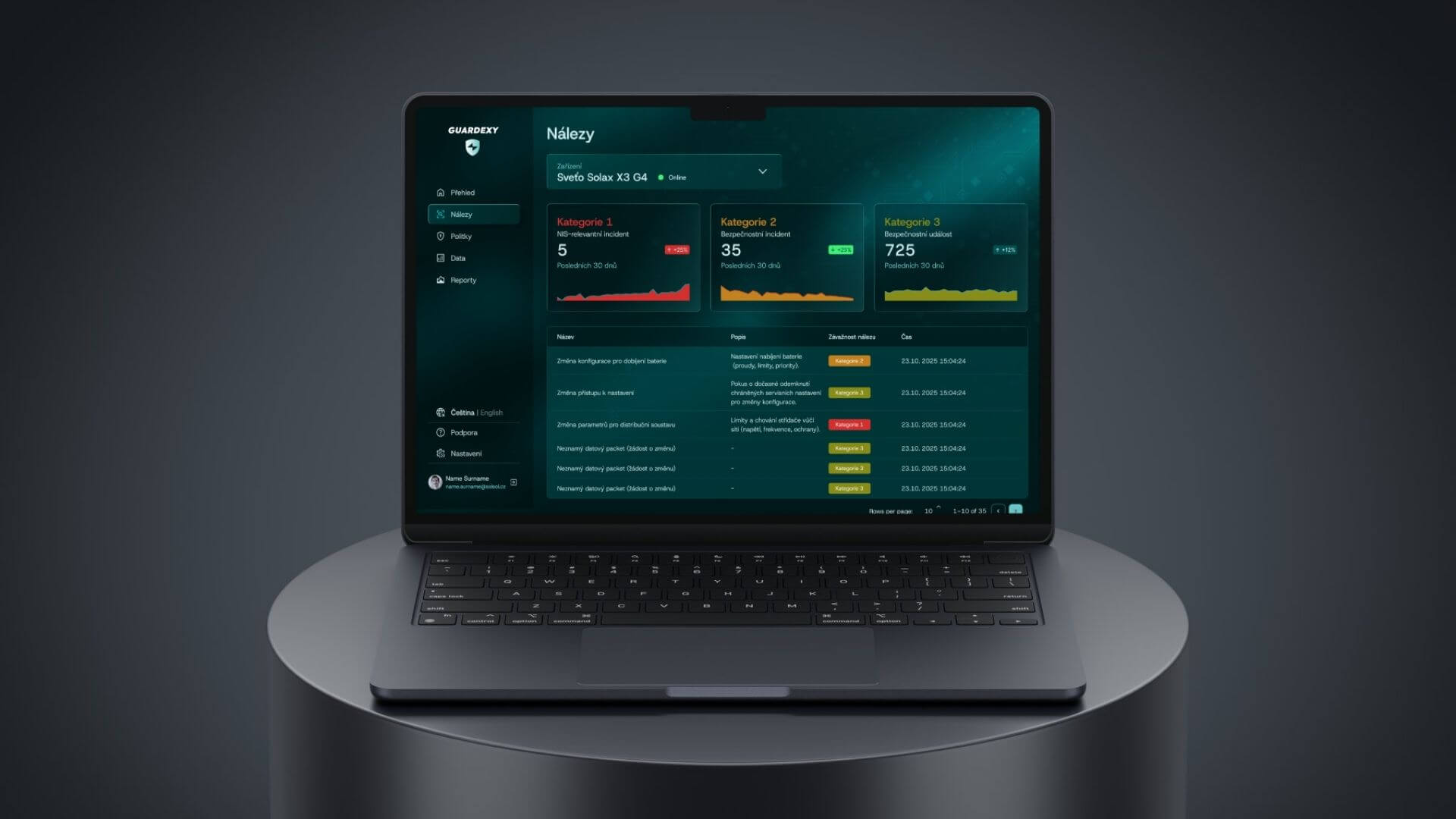
Therefore, starting in March, Guardexy is expanding the functionality of its solution. Alongside continuous monitoring of data flows, we are newly launching a monthly history of captured security events and incidents in the form of a structured report, which is prepared for internal audits as well as for official reporting needs.
Why incident logging is essential
NIS2 emphasizes not only prevention but also the organization’s ability to demonstrably:
- detect security events,
- evaluate their severity,
- take corrective measures,
- report significant incidents in a timely manner.
In practice, this means that mere “traffic logging” is no longer sufficient. A municipality or company must be able to document what happened, when, with what impact, and how the situation was resolved.
Guardexy: from monitoring to auditable reporting
Our solution has long monitored the communication of photovoltaic power plants. Now, however, we not only analyze data in real-time but also systematically archive and classify it.
The monthly report contains a history of captured events divided by severity, including information needed for internal security management and regulatory obligations.
Four levels of security events according to Guardexy
To correctly interpret and prioritize incidents, we are introducing a uniform classification of data packets and operations into four levels.
Protection Level | Description |
|---|---|
Level 0 – Allowed Event | Normal, expected, and legitimate traffic. Typically, this involves standard technology communication, for example:
· automated processes,
· scheduled operations,
· interventions by an authorized user or service,
· data reading (Read) or pre-approved changes (Write).
The event has no or negligible impact on operations. It is allowed and recorded only in aggregate for statistical purposes. |
Level 1 – Security Event
| A situation that deviates from standard behavior but does not represent a direct disruption of operations, typically:
· unclear or missing communication context,
· non-standard communication patterns,
· operations with limited impact,
· suspicious but harmless behavior.
The event is recorded in detail and displayed in the console as a security finding. It primarily serves for the early detection of potential risks. |
Level 2 – Mitigated Security Incident | At this level, an unauthorized intervention attempt occurs. Typical manifestations include:
· unauthorized configuration changes,
· attempts to control the device without authorization,
· Write or Control operations with significant impact.
Guardexy technically stops the incident (for example, by blocking communication or restricting access), and no actual disruption of operations occurs. The incident is recorded in the incident log and presented as a mitigated security incident. |
Ready for municipalities, cities, and enterprises
For the leadership of municipalities and companies, it is crucial that this categorization translates cybersecurity from a purely technical level into a clear managerial view of risks. The report clearly shows what is actually happening in the infrastructure, how severe the situations were, and which of them may have a regulatory impact. The organization thus gains not only protection but also conclusive documentation for audits, inspections, or crisis management.
For municipalities and cities, this is often the first tool that allows them to fulfill new obligations without the need to build their own security operations center.
NIS2 is not just about protection, but about accountability
Modern cybersecurity is no longer just a technical discipline. Equally important is the ability to demonstrate that the organization is proceeding systematically and responsibly.
Guardexy therefore elevates monitoring to the level of full-fledged security oversight with an audit trail, which helps protect not only the technology but also the organization’s leadership from regulatory risks from NÚKIB.
If you are unsure whether you fall under the mandatory entities, or if you want to be certain that your infrastructure meets the new requirements, please contact us.